Cybereason security researcher Amit Serper has found a way to prevent the Petya (NotPetya/SortaPetya/Petna) ransomware from infecting computers.
The ransomware has been wreaking havoc across the globe today, locking hard drive MFT and MBR sections and preventing computers from booting. Unless victims opted to pay a ransom (which is now pointless and not recommended), there was no way to recover their systems.
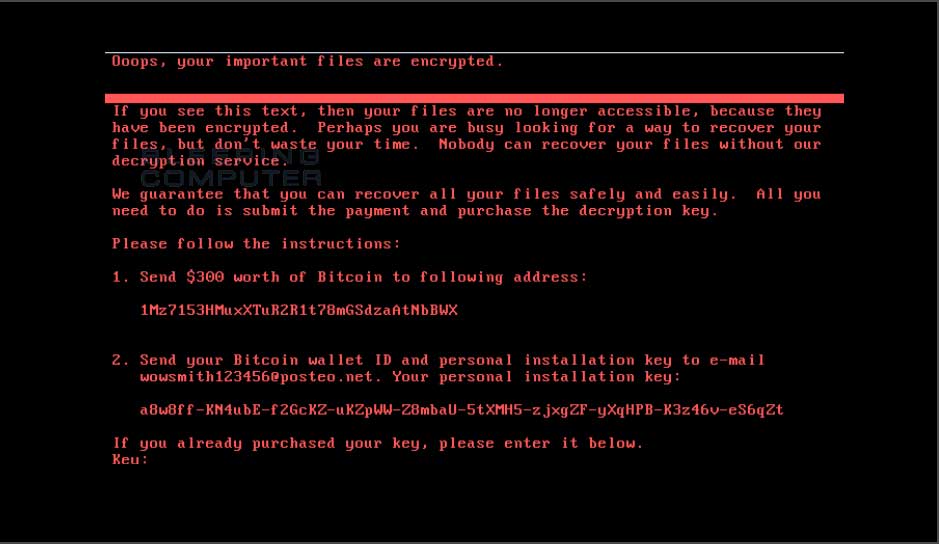
In the first hours of the attack, researchers believed this new ransomware was a new version of an older threat called Petya, but they later discovered that this was a new strain altogether, which borrowed some code from Petya, hence the reason why they recently started it calling it NotPetya, Petna, or as we like to call it SortaPetya.
Researchers flocked to find killswitch mechanism
Because of the ransomware's global outreach, many researchers flocked to analyze it, hoping to find a loophole in its encryption or a killswitch domain that would stop it from spreading, similar to WannaCry.
While analyzing the ransomware's inner workings, Serper was the first to discover that NotPetya would search for a local file and would exit its encryption routine if that file already existed on disk.
The researcher's initial findings have been later confirmed by other security researchers, such as PT Security, TrustedSec, and Emsisoft.
This means victims can create that file on their PCs, set it to read-only, and block the NotPetya ransomware from executing.
While this does prevent the ransomware from running, this method is more of a vaccination than a kill switch. This is because each computer user must independently create this file, compared to a "switch" that the ransomware developer could turn on to globally prevent all ransomware infections.
How to Enable the NotPetya/Petna/Petya Vaccine
To vaccinate your computer so that you are unable to get infected with the current strain of NotPetya/Petya/Petna (yeah, this naming is annoying), simply create a file called perfc in the C:\Windows folder and make it read only. For those who want a quick and easy way to perform this task, Lawrence Abrams has created a batch file that performs this step for you.
For those who want a little more control or native executable that can make these changes, I have created a new vaccinator. This is native executable with extra options that may make it easier for those who want to customize which vaccination files are created, to remove vaccination files, and to suppress output for those who wish to use it as part of a login script or another script.
The file can be downloaded from here: https://download.bleepingcomputer.com/vaccines/NotPetyaVaccine.exe
It is a command line tool that when run without command line arguments will just create the C:\Windows\perfc file and exits.
You can use the /h argument to see the full help file that contains info on how to customize its execution..
Please note that he batch file will also create two addition vaccination files called perfc.dat and perfc.dll. While my tests did not indicate that these additional files are needed, I added them for thoroughness based on the replies to this tweet.
This batch file can be found at: https://download.bleepingcomputer.com/bats/nopetyavac.bat
For those who wish to vaccinate their computer manually, you can do so using the following steps. Please note that these steps are being created to make it as easy as possible for those with little computer experience. For those who have greater experience, you can do it in quite a few, and probably better, ways.
First, configure Windows to show file extensions. For those who do not know how to do this, you can use this guide. Just make sure the Folder Options setting for Hide extensions for known file types is unchecked like below.

Once you have enabled the viewing of extensions, which you should always have enabled, open up the C:\Windows folder. Once the folder is open, scroll down till you see the notepad.exe program.
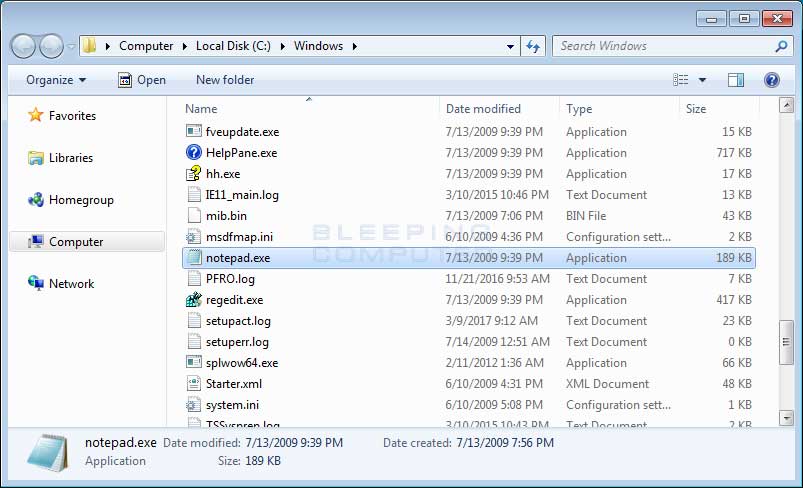
Once you see the notepad.exe program, left-click on it once so it is highlighted. Then press the Ctrl+C ( ![]() ) to copy and then Ctrl+V (
) to copy and then Ctrl+V ( ![]() ) to paste it. When you paste it, you will receive a prompt asking you to grant permission to copy the file.
) to paste it. When you paste it, you will receive a prompt asking you to grant permission to copy the file.
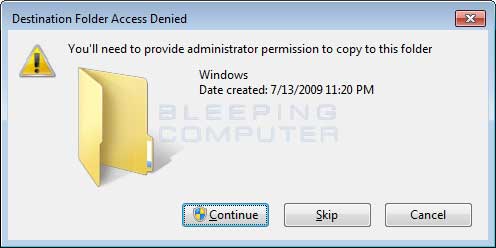
Press the Continue button and the file will be created as notepad - Copy.exe. Left click on this file and press the F2 key on your keyboard and now erase the notepad - Copy.exe file name and type perfc as shown below.
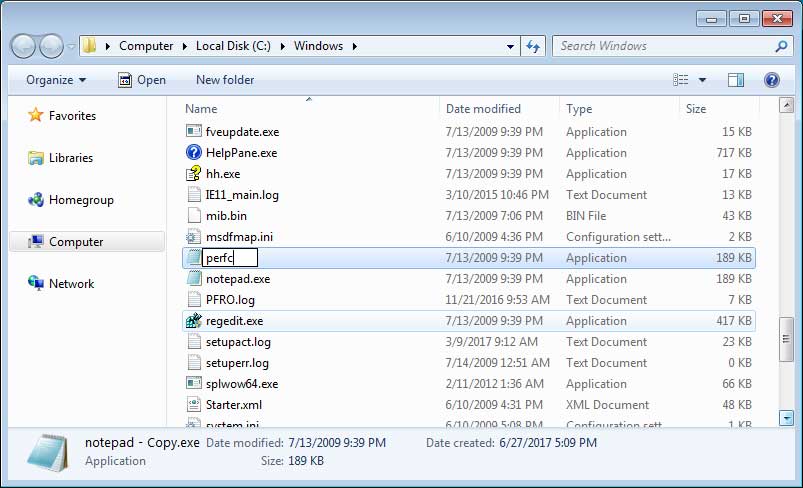
Once the filename has been changed to perfc, press Enter on your keyboard. You will now receive a prompt asking if you are sure you wish to rename it.
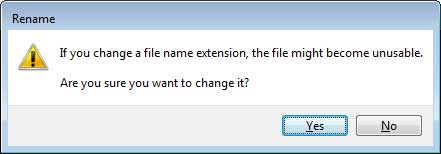
Click on the Yes button. Windows will once again ask for permission to rename a file in that folder. Click on the Continue button.
Now that the perfc file has been created, we now need to make it read only. To do that, right-click on the file and select Properties as shown below.
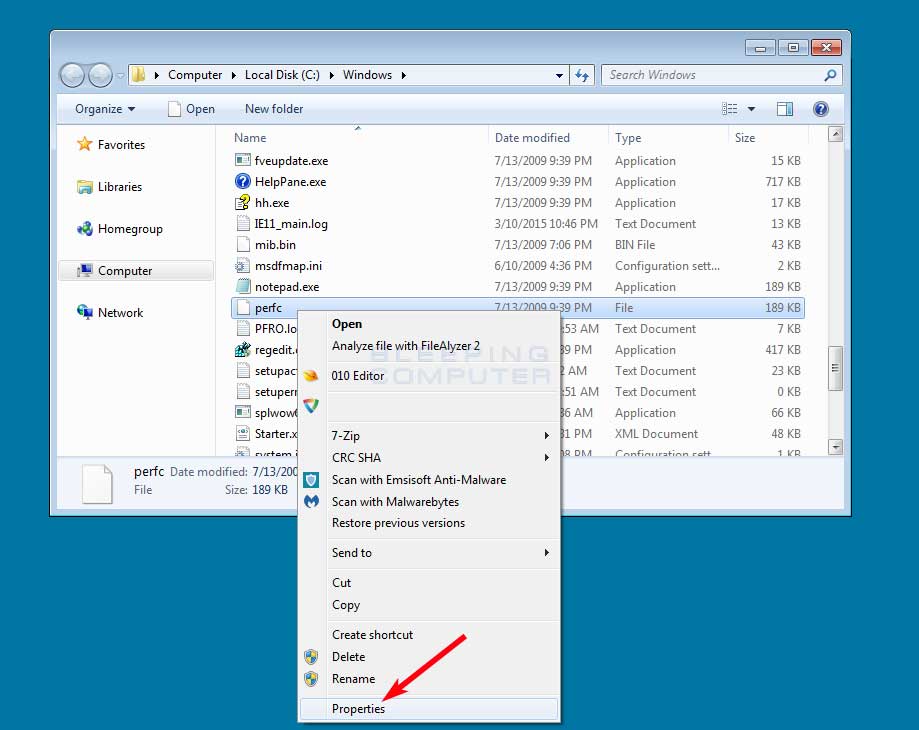
The properties menu for this file will now open. At the bottom will be a checkbox labeled Read-only. Put a checkmark in it as shown in the image below.
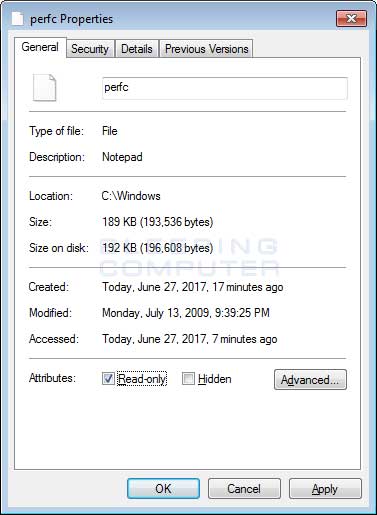
Now click on the Apply button and then the OK button. The properties Window should now close. While in my tests, the C:\windows\perfc file is all I needed to vaccinate my computer, it has also been suggested that you create C:\Windows\perfc.dat and C:\Windows\perfc.dll to be thorough. You can redo these steps for those vaccination files as well.
Your computer should now be vaccinated against the NotPetya/SortaPetya/Petya Ransomware.
Additional reporting by Lawrence Abrams.
6/28/17 8:26AM EST: This article has been updated to clarify in more detail how the batch script works
Bleeping Computer Petya/NotPetya coverage:
Surprise! NotPetya Is a Cyber-Weapon. It's Not Ransomware
Petya Ransomware Outbreak Originated in Ukraine via Tainted Accounting Software
Vaccine, not Killswitch, Found for Petya (NotPetya) Ransomware Outbreak
Email Provider Shuts Down Petya Inbox Preventing Victims From Recovering Files
WannaCry Déjà Vu: Petya Ransomware Outbreak Wreaking Havoc Across the Globe


Comments
Union_Thug - 6 years ago
Great work @LawrenceAbrams!
EddW - 6 years ago
Thanks for the excellent information. I have posted an extension to yours on how to deploy this using Group Policy https://eddwatton.wordpress.com/2017/06/27/use-group-policy-preferences-to-deploy-the-notpetya-vaccine/
iceman_7801 - 6 years ago
Hi guys
Great work on this, how many people have seen this and deployed, seems like firewall and AV prevents this from running plus you need to configure to run as Admin
Also wondering why the bat file has created the following files when the article above suggests just copying the notepad file and creating one file??
We are an MSP and have thousands of computers so I need to ensure there will be no issues :)
C:\windows
perfc
perfc.dat
perfc.dll
Lawrence Abrams - 6 years ago
I need to update the article. In my tests, just creating perfc works, but after reading various comments on Twitter, it was not 100% clear if that would work be enough for all variants. So I added perfc.dat, which is the name I have seen in the wild, and perfc.dll, which some reported as needed as well.
TheDcoder - 6 years ago
Kudos for making the batch script
ucmego - 6 years ago
So is the bat file stopping the virus from deploying?
TheDcoder - 6 years ago
Yeah, it creates some files which the ransomware checks before infecting
Lawrence Abrams - 6 years ago
Yes, when the DLL for NotPetya is executed it first checks for the existence of the perfc file. If it is detected, the process exits.
tos226 - 6 years ago
I did not use the batch file, and ran into a problem in one step:
- On Windows 7 my account is administrator. No problems to copy, paste, rename, set read only.
- On Windows 10 my account is limited/normal user. No problems copy, paste, rename (and enter admin password on each of those of course). BUT, setting read only failed with Access denied. I had to login to my admin account to be able to change properties.
Lawrence Abrams - 6 years ago
Good info. Will update the article to reflect this. The batch file should have worked, though, if you ran it as administrator.
You will need an administrator account with a password already created, though, and you will be prompted for these credentials.
WKdot80 - 6 years ago
iceman, you only need to create the one file, not three.
I work for an MSP as well. We deployed a script with our RMM, over 3000 computers done inside the hour.
iceman_7801 - 6 years ago
@ WKdot80 thanks for your reply, so you just deployed as per the article and not the batch file, how did you do this getting around AV and firewalls
Andre_Castillo14 - 6 years ago
You guys think it's a good idea for me to create the "Vaccine" and Update Windows 10 to the latest version? Those are the only options I got at the moment.
Since I just applied the so-called "Vaccine", what are the chances now that I will get infected by the RansomWare?
nenebird - 6 years ago
Great work guys!!! I ran the batch file and I also did the manual steps to make doubly sure. Redundant but safe. Thank you!!!
WKdot80 - 6 years ago
Do you know what an RMM is? We have agents deployed on every computer we monitor. The agents ran the file creation process for us. Took five minutes to deploy the file across all the computers. Any that are sleeping/turned off will create the file the next time they are turned on.
iceman_7801 - 6 years ago
@ Andre_Castillo14 as far as we know the Petya (NotPetya) Ransomware is still using the external blue exploit to spread Microsoft Security Bulletin MS17-010 - Critical - ensure that is patched and you don't have 445 SMB external facing, always ensure windows, AV and third party apps are updated.
I really don't seen any reason why you should not deploy the Vaccine even if you think you are protected, you will find ALL AV companies release definition files to patch this.
Andre_Castillo14 - 6 years ago
445 SMB is network related, right? If it is, I have no way to access my network settings since I'm locked out.
Regarding the Anti-Viruses patching the exploit, you think I can delete the perfc files after a few days/weeks or until we are given the clear signal?
ucmego - 6 years ago
Hi,
Other than file extension setting so do I se the bat file created and run it in admin mode and do nothing else?
Lawrence Abrams - 6 years ago
If you run the batch file, you do not need to do the manual steps at all. The showing of file extensions, which everyone should enable, is only necessary when you wish to manually create the files.
Nino66 - 6 years ago
Hi, I was wondering : why doing the perfc file with Notepad ?
Could it be done with any other executable file ?
Thx for the tip.
persmash - 6 years ago
"Hi, I was wondering : why doing the perfc file with Notepad ?
Could it be done with any other executable file ?
Thx for the tip."
Yes. You just need to create file.
Nino66 - 6 years ago
"Yes. You just need to create file."
Thx permash
I can't run the batch file because of Administrator's rights... but I am Admin !
Cauthon - 6 years ago
I used to have a problem like that with Windows 7, I was the original user of the computer, and mostly the only user, but from time to time I would get that kind of error message from the recreant demon in the machine, saying shut up and leave me alone you peon, I only obey administrators. I never really tried much to get rid of that, and haven't noticed it much in Win 10. I did find out one thing, the reason I get an error message when I click on "My Pictures" instead of just "Pictures" is that it isn't a real folder. I don't know what it does, or why it has to be visible, or why they could not have given it a different name (maybe "not pictures"?) but there it is. I recently got a new computer and when I set up the files on that one maybe I can name the folder for pictures "REAL PICTURES" or some such.
simondh - 6 years ago
There seems to be some confusion as to the files required here. The batch file creates 3 files of 1Kb each with the text "This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. " The files are perfc, perfc.dat and perfc.dll. The instructions here only create 1 file. It is probably safer to create the 3 files until this is cleared up as perfc on its own may not be enough.
Lawrence Abrams - 6 years ago
See comments above. I added the other two to be safe, but my tests only required the perfc file. Having the other two do not cause any issues though.
simondh - 6 years ago
There's a lot of info on github
https://gist.github.com/vulnersCom/65fe44d27d29d7a5de4c176baba45759
Maybe blocking the 4 ip addresses listed there on your router or firewall
185.165.29.78
84.200.16.242
111.90.139.247
95.141.115.108
and also url filter blocking the domains french-cooking.com and coffeinoffice.xyz
JasonRyan - 6 years ago
If you're deploying across multiple windows machines you're better off creating a batch file with the following:
cd C:\Windows
copy NUL perfc
attrib R perfc
We used Desktop Central to deploy it.
Edit: I'm an idiot, missed that line in the article, ha.
sympology - 6 years ago
I've been doing a lot of reading, so a few points.
1. It does NOT stop you getting infected. It stops you getting encrypted. That is all.
2. Many filewalls, AV and even windows will stop you downloading and running .bat files. A very sensible choice as it's the most simple way of messing up a machine.
3. Many email systems will prevent you emailing .bat files.
4 Windows is a protected folder, you often cannot create files in there directly.
Here is another way of doing it.
Open a cmd prompt with Admin permissions. On windows 8 onwards, Right click the "start" button and click on Command Prompt(Admin). On Windows 7 Left click on Start button, >All Programmes > Accessories and Right Click on Command prompt and select "Run As Administrator (click Yes)
Run this command
fsutil file createnew c:\windows\perfc.dat 1000
It should say file is created
now run
attrib R C:\Windows\perfc.dat
You should now have the correct file as read only.
Marcelhh - 6 years ago
Sorry to ask but, I only found that the perfc is needed: Why the cmd creates the other two files and what is their purchase?
Thx in advanced for having me informed.
Lawrence Abrams - 6 years ago
See my other replies. Perfc is only needed. The other two are to be thorough and cause no issues on the computer.
MindSmith - 6 years ago
After running the nopetyavac batch file Kaspersky detects the newly created perfc.dat file as being malicious and deletes it. Any other AntiViruses out there giving similar issues?
Marcelhh - 6 years ago
"After running the nopetyavac batch file Kaspersky detects the newly created perfc.dat file as being malicious and deletes it. Any other AntiViruses out there giving similar issues?"
We use "Trend Micro Office Scan" with latest pattern file: 13.499 and I did not receive any information about being malicious after running batch file.
herbgold - 6 years ago
"After running the nopetyavac batch file Kaspersky detects the newly created perfc.dat file as being malicious and deletes it. Any other AntiViruses out there giving similar issues?"
Yes, but it allows perfc and perfc.dll
herbgold - 6 years ago
Thanks to everyone above for a very helpful discussion. I have created three files in C:\WINDOWS by simply running an elevated notepad to create perfc, perfc.dll and perfc.dat as empty files and then running an elevated CMD to give the files a R attribute. Two questions:
1. The method used of copying notepad.exe to perfc worries me, because perfc will still be an executable file even though it has no .exe extension
2. Do we know if the malware looks for the files' EXISTENCE, or their CONTENTS.
cmckeown - 6 years ago
Any mind readers out there who have figured out why the creators of this virus crafted their code to not work if it detected the perfc files?
Lawrence Abrams - 6 years ago
Maybe to avoid double encryption.
Cauthon - 6 years ago
As the Old Harry used to say, all I know is what I read in the newspapers. I did see something in the newspaper a while ago saying that when our people at Fort Detrich were inventing better biological weapons they liked to have a vaccine so Captain Trips would not get them too. Seems to me the same thing might apply here, the perps wanted to protect their own equipment in case what goes around might come around - otherwise I see no reason why something that travels randomly all over the place could not go right back to where it came from.
Cauthon - 6 years ago
And, apparently from anything I have read here or any previous experience, the file we need and its name are not anything we would commonly find on a computer - no reason someone could not have used the name before but it is not something we would expect to find, until now. And the visitor does not use the file as part of its encryption or communication - that file exists only as a signal to stop. I.e., the writer wanted that function, because that is the only thing that file does. Meanwhile, just when we are all in danger and we should be circling the wagons and keeping our powder dry, and we should be thankful for this site and any other social sites that enable us to share information, the Bleeping Europeans are fining Google, lots of money, because they don't like how it works. I'm not sure I like everything Google does, and often I use some other search engine just to avoid them, and I may not always furnish truthful information when a site asks for it (those of you who know Matrim Cauthon may have guessed that I am an impostor, not the real hornsounder:-). Probably some community effort at improving tactics like that will do more good than this thievery by the bumbling government. So much for my 2 cents, time to get out of here and go have a few drinks with Birgitte and Thom.
Yojji - 6 years ago
An earlier article mentions that "...the NotPetya ransomware also uses two NSA exploits leaked by the Shadow Brokers in April 2017. These are ETERNALBLUE (also used by WannaCry) and ETERNALROMANCE." I think Microsoft has already issued patches for the vulnerabilities exploited by these tools. Does this mean that Petya(NotPetya) cannot infect an up-to-date Windows installation?
Lawrence Abrams - 6 years ago
It can target machines laterally without the EternalBlue exploit. It tries to use WMIC and psexec files to spread throughout a network.
Yojji - 6 years ago
Thank you, Grinler.
jflemelin - 6 years ago
Cheers, thanks for the well explained article.
glnz - 6 years ago
Dear Bleeping -
Please give us a DEFINITIVE answer whether we need anything more than one read-only "perfc" in C:\Windows.
Thanks for article, but there is some confusion.
Lawrence Abrams - 6 years ago
C:\windows\perfc should be good enough for now.
Lawrence Abrams - 6 years ago
In my tests, you only need the perfc. I will be releasing a new tool that is easier to use in a bit.
Lawrence Abrams - 6 years ago
I have created a new vaccinator to help those who have been having issues with the batch file. This is native executable with extra options that may make it easier for those who want to customize which vaccination files are created, to remove vaccination files, and to suppress output for those who wish to use it as part of a login script or another script.
The file can be downloaded from here: https://download.bleepingcomputer.com/vaccines/NotPetyaVaccine.exe
It is a command line tool and by default only creates the C:\Windows\perfc vaccination file.
If you run it without command line args, it just creates the C:\Windows\perfc file and exits.
You can use the /h argument to see the full help file that contains info on how to customize its execution..
I would appreciate it if people could test the exec and provide feedback.
johnd0e8 - 6 years ago
Works great for me. Thanks!
Cauthon - 6 years ago
All I know is that I created the first file this morning, and later when I had a little time I copied it and renamed the copies to have the other 2 just in case, and I have not seen any mushroom-shaped clouds coming out of my computer so far:-) I really appreciate all the work that better people than I have done to get us out of this mess. I hope some of them are watching to see if the perps change the file so our vaccine would stop working. Meanwhile I have told Avast to go see what it can find in my computer.
Kronks2 - 6 years ago
"I have created a new vaccinator to help those who have been having issues with the batch file. This is native executable with extra options that may make it easier for those who want to customize which vaccination files are created, to remove vaccination files, and to suppress output for those who wish to use it as part of a login script or another script.
The file can be downloaded from here: https://download.bleepingcomputer.com/vaccines/NotPetyaVaccine.exe
It is a command line tool and by default only creates the C:\Windows\perfc vaccination file.
If you run it without command line args, it just creates the C:\Windows\perfc file and exits.
You can use the /h argument to see the full help file that contains info on how to customize its execution..
I would appreciate it if people could test the exec and provide feedback."
I would never download and run an executable from you , how do I know it is the not randomware executable?
I think you are reckless and disturbing.
Lawrence Abrams - 6 years ago
I think I, and my site, have built a reputation over the years that can be trusted. BleepingComputer has released numerous executables over the past 14 years that have helped countless people.
If you choose to not trust me, and therefore BleepingComputer, then do not download the exec. Simple as that.
digital_punk - 6 years ago
the perfc file should be also enough for blocking the encryption on M$ server 2008 and 2012, right?
for xen server hypervisor virtual instances its also a quick fix or isn"t it?
Lawrence Abrams - 6 years ago
Shouldn't matter what OS. Does appear that the C:\Windows was hard coded, so if you use a non-standard %WinDir% you would want to create a C:\WIndows folder and put the file there.
digital_punk - 6 years ago
thanks, more questions follow...
can you confirm, that there is an exact hour delay between infection and force restart?
Boris900 - 6 years ago
Hello, many thanks for your help!
We have some MAC in the office, does it work with their OS?
Boris900 - 6 years ago
and Linux?
Lawrence Abrams - 6 years ago
Macs and Linux are safe from this particular threat.
digital_punk - 6 years ago
As I was informed the MBR is infected and a timer for force reboot is set.
After restart MBR is executed and encryption is triggered on the file table.
How does the perfc block the decryption in this moment?
Does it just check the existence of the file?
----------------------------------------------------------------------
I just read last reply... hard coded.... all clear!
But what about the trigger?
Lawrence Abrams - 6 years ago
If the file is present, the dll simply unloads before doing anything.
Otherwise it performs a file encryption while windows is running on a limited set of files. It also creates a task that reboots the computer in about 60ish minutes. Once rebooted it goes into the MFT encryption stage.
Kronks2 - 6 years ago
"As I was informed the MBR is infected and a timer for force reboot is set.
After restart MBR is executed and encryption is triggered on the file table.
How does the perfc block the decryption in this moment?
Does it just check the existence of the file?
----------------------------------------------------------------------
I just read last reply... hard coded.... all clear!
But what about the trigger?"
====================
HI!!!!!!!!! Of if the the thing is run after reboot then power off and take out the drive and then you can back up the file on it of chance it so it does not encrtypt
iceman_7801 - 6 years ago
@ Grinler just wondering the only way this virus can penetrate the network is if you have SMB v1 (445) internet facing to the world and I think many people don't, however, once it gains access to the network it uses WMIC an psexec to spread throughout?
do you have this virus and testing in a sand box or something, where are you getting your information from?
thanks again really appreciate your input
Lawrence Abrams - 6 years ago
Correct. Yes, I test every ransomware I write about at BleepingComputer, which is about every one that's been released. From what I understand its SMB v1 spread is low. See here: for info on lateral spreading: https://blog.kryptoslogic.com/malware/2017/06/28/petya.html
Kronks2 - 6 years ago
This is the contents of the batch fie For those interested it was hard work getting them cos the download is a batch file and my computer will only let me run if until I modified some setting. Also it does not display well in notepad as it is workpad format which fucks up the format. So basally you need to create the three files (perfc, ,perfc.dat, perfc.dll) as admin and make them read only. The contexts were between the ============ lines
===============================
@echo off
REM Administrative check from here: https://stackoverflow.com/questions/4051883/batch-script-how-to-check-for-admin-rights
REM Vaccination discovered by twitter.com/0xAmit/status/879778335286452224
REM Batch file created by Lawrence Abrams of BleepingComputer.com. @bleepincomputer @lawrenceabrams
echo Administrative permissions required. Detecting permissions...
echo.
net session >nul 2>&1
if %errorLevel% == 0 (
if exist C:\Windows\perfc (
echo Computer already vaccinated for NotPetya/Petya/Petna/SortaPetya.
echo.
) else (
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc.d
ll
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc.d
at
attrib +R C:\Windows\perfc
attrib +R C:\Windows\perfc.dll
attrib +R C:\Windows\perfc.dat
echo Computer vaccinated for current version of NotPetya/Petya/Petna/SortaPetya.
echo.
)
) else (
echo Failure: You must run this batch file as Administrator.
)
pause
=================
so just create those 3 in the windows folder as readonly as admin.
Lawrence Abrams - 6 years ago
Yup, that's all the batch file does. The rest is to make sure the batch runs Administrative privileges as you need that in order to have write permissions for the Windows folder.
JustineCause - 6 years ago
Kronks2, having played around with batch files in the early '80s I thought I would give yours and of course Lawrence Abrams work a try :)
Interestingly I found a couple of bugs that are probably specific to my version of Windoz 7 Home Premium [Version 6.1.7601].
First, "echo." doesn't work, so I changed those to "echo off" .
Second, "attrib R C:\Windows\perfc" didn't change the file to read only, so I had to add a plus sign before the R "attrib R C:\Windows\perfc" . HMMM OK, FOR SOME REASON THE COMMENT PROGRAM ON THIS SITE REMOVES THE PLUS SIGN IN FRONT OF A CAPITAL R... Weird
Then I added the line "attrib C:\Windows\perfc.*" for confirmation ;)
Here's my version:
===============================
REM Administrative check from here: https://stackoverflow.com/questions/4051883/batch-script-how-to-check-for-admin-rights
REM Vaccination discovered by twitter.com/0xAmit/status/879778335286452224
REM Batch file created by Lawrence Abrams of BleepingComputer.com. @bleepincomputer @lawrenceabrams
echo Administrative permissions required. Detecting permissions...
echo off
net session >nul 2>&1
if %errorLevel% == 0 (
if exist C:\Windows\perfc (
echo Computer already vaccinated for NotPetya/Petya/Petna/SortaPetya.
echo off
) else (
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc.dll
echo This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya. > C:\Windows\perfc.dat
REM ADD A PLUS SIGN IN FRONT OF THE R ON THE NEXT 3 LINES
attrib R C:\Windows\perfc
attrib R C:\Windows\perfc.dll
attrib R C:\Windows\perfc.dat
attrib C:\Windows\perfc.*
echo Computer vaccinated for current version of NotPetya/Petya/Petna/SortaPetya.
echo off
)
) else (
echo Failure: You must run this batch file as Administrator.
)
pause
======================================
Lawrence Abrams - 6 years ago
That was my batch file that he copied. Unfortunately, he did not copy it correctly so it will not work as there are missing characters.
JustineCause - 6 years ago
Apparently the comment program on this website doesn't allow the character PLUS SIGN, go figure
Kronks2 - 6 years ago
"Apparently the comment program on this website doesn't allow the character PLUS SIGN, go figure"
what do you mean by "the comment" program? ??????
JustineCause - 6 years ago
OK, It seems to work with my mods. And I bothered, finally, to check that stackoverflow.com link in the REMs and learnt sumpin YaY
Kronks2 - 6 years ago
"That was my batch file that he copied. Unfortunately, he did not copy it correctly so it will not work as there are missing characters."
The file is in doc format, why?
I copied and pasted it, as it is .doc file that may not have worked too well
Why didn't you use a text file? That is a lot simpler and avoid format and all sorts of potential problems..
As for later providing an executable, well I certainly am not running an executable which could actually be the randsomware program itself..
I have the word of one person who I do not know that it is safe. That is not good enough for me. I do not consider it safe and I am not putting my computer at risk running unverified code.
Cauthon - 6 years ago
The old folks used to have a saying, don't look in the mouth of a gift horse (don't be visibly ungrateful for a gift). Seems that we young folks could profit from that principle. I am sticking by my comment of yesterday, I followed the advice, created the files, and have not seen any problems - could be just luck that the devil has not caught up with me, or the protection is working, I am keeping the files just in case - and I appreciate the information. :-)
JustineCause - 6 years ago
Well allrighty then, due to the screwed up way this website posts simple text files with all adding and subtracting of characters (net session >nul 2>&1 SERIOUSLY? What The FUCK?) You might as well delete all my posts And my account. I'm not bothering with this anymore...
And I am in no way admitting I completely forgot what echo. did lol
JustineCause - 6 years ago
just so you know, this websites posting system edited this "net session >nul 2>&1" once again when I edited my comment above. I had to go back and edit it again. HOW SCREWED UP IS THAT?
IllusionEclipse - 6 years ago
For some reason after applying the vaccine last night. I booted up my computer, logged in like usual. Then after about 10 minutes my laptop completely froze up. Removing the created files fixed the issue. Which does have me somewhat concerned whether there is a problem with the batch file, any of the 3 individual files or just my laptop having an issue with them.
Running Windows 7 64Bit on a Dell Inspiron 3000 Series Laptop.
Kronks2 - 6 years ago
plus sign test
Failed, so I cannot write a plus sign in the comments - now utterly ridiculous,
How the hell can that happen?
Is there a line in the program to remove plus signs?
Again that is just unbelievable.
Kronks2 - 6 years ago
and I cannot edit my previous comment to say what I copied probably failed to *display* properly.
Kronks2 - 6 years ago
So I or anyone could post advice here and the advice displayed might not be the advice given
that is shocking.
IT IS NOT SAFE.
The problem it sees it not to do with the copy but rather an inexplicable failure to display posts as intended.
Someone has do specifically write code not to display plus signs, why?
It would not happen by accident.
Lawrence Abrams - 6 years ago
It's all good. You found a bug. I appreciate it. This bug is fixed.
10+10 = 20
Kronks2 - 6 years ago
Recall the source of the problem is Microsoft.
There software cannot have so many vulnerabilities by accident.
They must be putting them either in of their own choice or at request of the "security services".
Really Windows should be binned and a public funded Linux version should be made available
with open source.
Kronks2 - 6 years ago
Everything there now?
32 20 00100000 Space space
33 21 00100001 ! exclamation mark
34 22 00100010 " double quote
35 23 00100011 # number
36 24 00100100 $ dollar
37 25 00100101 % percent
38 26 00100110 & ampersand
39 27 00100111 ' single quote
40 28 00101000 ( left parenthesis
41 29 00101001 ) right parenthesis
42 2A 00101010 * asterisk
43 2B 00101011 + plus
44 2C 00101100 , comma
45 2D 00101101 - minus
46 2E 00101110 . period
47 2F 00101111 / slash
48 30 00110000 0 zero
49 31 00110001 1 one
50 32 00110010 2 two
51 33 00110011 3 three
52 34 00110100 4 four
53 35 00110101 5 five
54 36 00110110 6 six
55 37 00110111 7 seven
56 38 00111000 8 eight
57 39 00111001 9 nine
58 3A 00111010 : colon
59 3B 00111011 ; semicolon
60 3C 00111100 < less than
61 3D 00111101 = equality sign
62 3E 00111110 > greater than
63 3F 00111111 ? question mark
64 40 01000000 @ at sign
65 41 01000001 A
66 42 01000010 B
67 43 01000011 C
68 44 01000100 D
69 45 01000101 E
70 46 01000110 F
71 47 01000111 G
72 48 01001000 H
73 49 01001001 I
74 4A 01001010 J
75 4B 01001011 K
76 4C 01001100 L
77 4D 01001101 M
78 4E 01001110 N
79 4F 01001111 O
80 50 01010000 P
81 51 01010001 Q
82 52 01010010 R
83 53 01010011 S
84 54 01010100 T
85 55 01010101 U
86 56 01010110 V
87 57 01010111 W
88 58 01011000 X
89 59 01011001 Y
90 5A 01011010 Z
91 5B 01011011 [ left square bracket
92 5C 01011100 \ backslash
93 5D 01011101 ] right square bracket
94 5E 01011110 ^ caret / circumflex
95 5F 01011111 _ underscore
96 60 01100000 ` grave / accent
97 61 01100001 a
98 62 01100010 b
99 63 01100011 c
100 64 01100100 d
101 65 01100101 e
102 66 01100110 f
103 67 01100111 g
104 68 01101000 h
105 69 01101001 i
106 6A 01101010 j
107 6B 01101011 k
108 6C 01101100 l
109 6D 01101101 m
110 6E 01101110 n
111 6F 01101111 o
112 70 01110000 p
113 71 01110001 q
114 72 01110010 r
115 73 01110011 s
116 74 01110100 t
117 75 01110101 u
118 76 01110110 v
119 77 01110111 w
120 78 01111000 x
121 79 01111001 y
122 7A 01111010 z
123 7B 01111011 { left curly bracket
124 7C 01111100 | vertical bar
125 7D 01111101 } right curly bracket
126 7E 01111110 ~ tilde
127 7F 01111111 DEL delete
Ryan87 - 6 years ago
I created my own batch file that also renamed the vssadmin.exe utility to something else, therefore removing the Ransomwares ability to delete shadow copies, inturn allowing me to restore my files :)
My not be the best batch file, but it works for what I want it to do.
Must Be Ran As Admin
=======
::Set VSSADMIN File Path
SET VssAdmin="c:\windows\system32\vssadmin.exe"
SET VssAdminNew="vssadmin_Clean.exe"
SET VssAdminClean="c:\windows\system32\vssadmin_Clean.exe"
::Rename VSSADMIN If Exists
IF EXIST %VssAdminClean% goto Petya
IF EXIST %VssAdmin% takeown /F %VssAdmin%
IF EXIST %VssAdmin% icacls %VssAdmin% /grant Administrators:(F)
IF EXIST %VssAdmin% ren %VssAdmin% %VssAdminNew%
:Petya
::Set Path To Petya Vaccine Files
SET Perfc="c:\windows\perfc"
SET PerfcDat="c:\windows\perfc.dat"
SET PerfcDll="c:\windows\perfc.dll"
::Create Petya Vaccine Files If Not Exist
IF EXIST %Perfc% exit
IF EXIST %PerfcDll% exit
IF EXIST %PerfcDat% exit
echo "This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya." > C:\Windows\perfc
attrib +R C:\Windows\perfc
echo "This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya." > C:\Windows\perfc.dll
attrib +R C:\Windows\perfc.dll
echo "This is a NotPetya/Petya/Petna/SortaPetya Vaccination file. Do not remove as it protects you from being encrypted by Petya." > C:\Windows\perfc.dat
attrib +R C:\Windows\perfc.dat
exit
=====
jimmyj08 - 6 years ago
I have no idea if this will work but when you are lazy and don' t know any better, you try short cuts. Be sure to post if you think it will not work so others don't follow.
I took a picture file /jpg on my desktop and renamed it to perfc.exe. Then went to the properties to confirm a true exe file and made it read only. I then copied it two more times on the desktop and renamed each perfc.dll and and perfc.dat. I then went to the explorer and pasted the three into the windows file. probably a total time of 3 minutes total but will it work? I was concerned about taking a real .exe file and renaming it. In any case, I really appreciate your research, education and willingness to share- thank you.
Maxwell_Asin - 6 years ago
Why should we use Notepad.exe? Not Another file, example: Right Click and choose new text document and change its name?
Lawrence Abrams - 6 years ago
You can use whatever file you want. It's easier to just use the batch file or the executable I made as it will just be a small text file that is created. The instructions to use notepad were done to just make it as easy as possible for those who may not be familiar with windows.
gioversa - 6 years ago
Have you read this http://blog.ensilo.com/the-notpetya-not-killswitch ? I don't know what to think about it.